Security is an ongoing endeavor, and Apple has unveiled its newest solution for safeguarding iMessage today. iOS 17.4 beta now includes a cutting-edge post-quantum cryptography technique named PQ3. The new version enhances iMessage’s security features, making it the most secure texting protocol globally. The significance of iMessage quantum security both presently and in the future, the functionality of PQ3, and further details are discussed.
iMessage is known for its robust security measures. Apple has continuously enhanced iMessage security since its inception in 2011, starting with end-to-end encryption, adopting Elliptic Curve cryptography in 2019, introducing BlastDoor with iOS 14, and implementing Contact Key Verification by the end of 2023.
Apple has introduced a major cryptographic security enhancement for iMessage by completely rebuilding the system’s protocol. Apple provided a lengthy update on its Security Research blog this morning.
Today we are announcing the most significant cryptographic security upgrade in iMessage history with the introduction of PQ3, a groundbreaking post-quantum cryptographic protocol that advances the state of the art of end-to-end secure messaging. With compromise-resilient encryption and extensive defenses against even highly sophisticated quantum attacks, PQ3 is the first messaging protocol to reach what we call Level 3 security — providing protocol protections that surpass those in all other widely deployed messaging apps. To our knowledge, PQ3 has the strongest security properties of any at-scale messaging protocol in the world.
Apple Security Research Blog
Quantum security for iMessage
Signal was the first large-scale messaging network to introduce a post-quantum cryptography (PQC) security improvement last autumn, utilizing a “key establishment” process.
Apple’s security strategy includes two layers of protection: PQC key setup and continuous PQC rekeying.
There is no established industry standard for comparing classical and post-quantum cryptography systems, prompting Apple to create its own rating system. This is the appearance and the reason why PQ3 is named as a level 3 PQC.
iMessage on iOS 17.4 offers quantum safety at advanced levels.
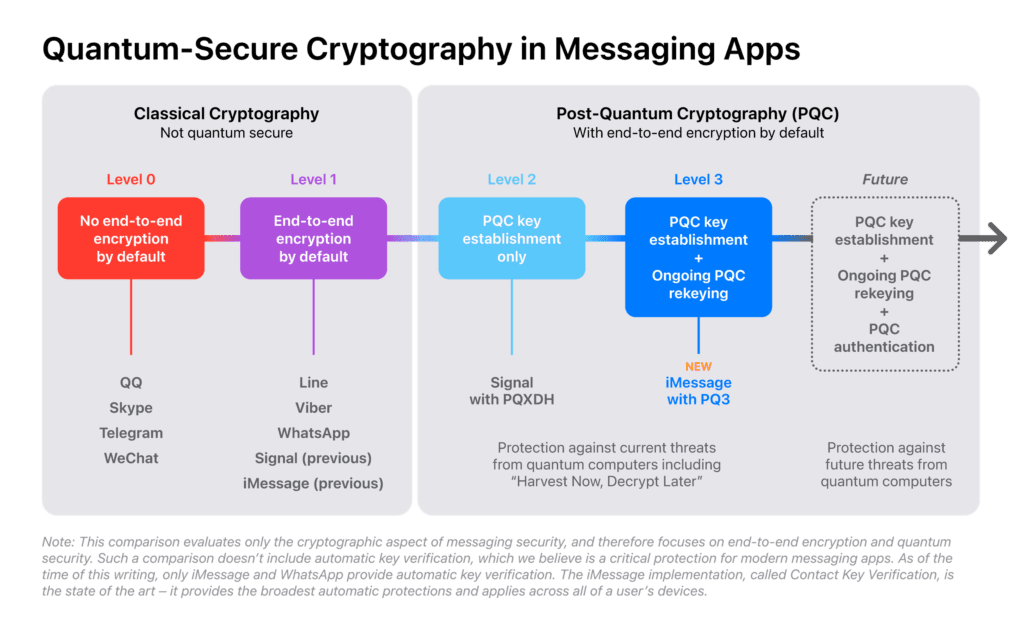
Apple acknowledges Signal’s implementation of PQC key setup (level 2) as a significant advancement that has elevated its security above that of rival messaging services. It can provide quantum security only provided the encryption key used in the communication remains secure.
At Level 2, post-quantum cryptography is used just for the first key establishment to ensure quantum security as long as the key material remains secure. Today’s advanced attackers are motivated to breach encryption keys in order to decrypt messages that are secured by those keys until they are changed. For optimal security in end-to-end encrypted communications, it is crucial to regularly update post-quantum keys to limit the potential exposure of conversations in case of a key compromise, both currently and in the future with quantum computers.
Apple’s PQ3 (level 3) protocol ensures the security of both the initial key and subsequent rekeying. iMessage has the capability to quickly and automatically restore the cryptographic security of a communication in case a key is compromised.
Apple foresees that future quantum security measures will involve Post-Quantum Cryptography (PQC) authentication, PQC key establishment, and continuous rekeying.
What is the current significance of post-quantum cryptography?
Many security experts predict that it will take at least a decade or more to fully realize the potential of quantum computers, such as breaking classical encryption. However, it is crucial to implement preventive measures now to safeguard current data from future threats.
Apple has identified a harmful strategy known as “Harvest Now, Decrypt Later,” which PQ3 will assist in safeguarding against.
A quantum computer with significant computational capabilities might potentially answer these traditional mathematical problems using fundamentally distinct methods, which could theoretically compromise the security of end-to-end encrypted communications due to its speed.
Despite the absence of quantum computers, well-funded attackers might prepare for their potential emergence by using the significant reduction in contemporary data storage expenses. The concept is straightforward: attackers can gather significant quantities of encrypted data and store it for later use. Although unable to decrypt the data currently, they can store it for future decryption using a quantum computer, a tactic known as Harvest Now, Decrypt Later.
Having advanced security measures in place can assist prevent current and future quantum attacks, as well as decryption attempts on stolen data from the past, as quantum computers become more prevalent.
When will iMessage quantum security be launched?
To enhance your iMessage experience, you can upgrade by installing the iOS 17.4 beta, along with the iPadOS 17.4, macOS 14.4, and watchOS 10.4 betas.
PQ3 quantum security for iMessage will be available to all users upon the public release of iOS 17.4, iPadOS 17.4, macOS 14.4, and watchOS 10.4.
Apple has stated that iMessage exchanges between devices that are compatible with PQ3 are transitioning to the post-quantum encryption protocol automatically.
The PQ3 protocol will completely replace the current protocol in all supported chats this year.
Further information regarding iMessage quantum security (PQ3)
Apple has five requirements for building PQ3.
👉🏻 Initiate discussions on post-quantum cryptography at the outset to ensure that all communications are safeguarded against present and future threats.
👉🏻 Reduce the consequences of key compromises by restricting the number of messages that may be decrypted with a single compromised key, both past and future.
👉🏻 Implement a hybrid design merging new post-quantum algorithms with current Elliptic Curve algorithms to guarantee that PQ3’s security level is always at least as strong as the current classical protocol.
👉🏻 Adjust message size to prevent excessive additional overhead caused by increased security measures.
👉🏻 Utilize formal verification methods to ensure robust security guarantees for the new protocol.
Here are some details regarding the post-quantum cryptography public keys that Apple is utilizing:
PQ3 introduces a new post-quantum encryption key in the set of public keys each device generates locally and transmits to Apple servers as part of iMessage registration. For this application, we chose to use Kyber post-quantum public keys, an algorithm that received close scrutiny from the global cryptography community, and was selected by NIST as the Module Lattice-based Key Encapsulation Mechanism standard, or ML-KEM. This enables sender devices to obtain a receiver’s public keys and generate post-quantum encryption keys for the very first message, even if the receiver is offline. We refer to this as initial key establishment.
Apple Security Blog
Professor David Basin, a senior figure in the Information Security Group at ETH Zürich and one of the creators of Tamarin, a prominent security protocol verification tool, has provided two formal verifications for PQ3.
Professor Douglas Stebila from the University of Waterloo, with significant expertise in post-quantum security for internet protocols, has officially certified PQ3.
Visit Apple’s comprehensive article on PQ3 quantum security for iMessage to go into the technical aspects of PQC key establishment, PQC rekeying, padding and encryption, authentication, and other related topics.